By Michele Kambas and James Pearson
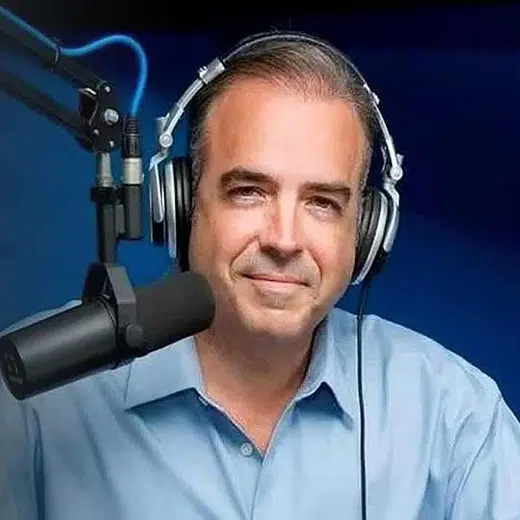
NICOSIA/LONDON (Reuters) – A 24-year-old videogame designer who runs his small business out of a home next to an old Cypriot church in a quiet suburb of Nicosia now finds himself entangled in a global crisis following the Russian invasion of Ukraine.
Polis Trachonitis’ firm, Hermetica Digital Ltd, has been implicated by U.S. researchers in a data-shredding cyberattack that hit hundreds of computers in Ukraine, Lithuania, and Latvia.
Discovered on Wednesday night just hours before Russian troops rolled into Ukraine, the cyberattack was widely seen as the opening salvo of Moscow’s invasion.
The malware had been signed using a digital certificate with Hermetica Digital’s name on it, according to the researchers, some of whom have started calling the malicious code “HermeticWiper” because of the connection.
Trachonitis told Reuters he had nothing to do with the attack. He said he never sought a digital certificate and had no idea one had been issued to his firm.
He said his role in the videogame industry is just to write the text for games that others put together.
“I don’t even write the code – I write stories,” he said, adding that he was unaware of the connection between his firm and the Russian invasion until he was told by a Reuters reporter on Thursday morning.
“I’m just a Cypriot guy … I have no link to Russia.”
The extent of the damage caused by the malware attack was not clear, but cybersecurity firm ESET said the malicious code had been found installed on “hundreds of machines”.
Western leaders have warned for months that Russia could conduct destructive cyberattacks against Ukraine ahead of an invasion.
Last week, Britain and the United States said Russian military hackers were behind a spate of distributed denial of service (DDoS) attacks that briefly knocked Ukrainian banking and government websites offline.
DIGITAL CERTIFICATE
Cyber spies routinely steal random strangers’ identities to rent server space, or register malicious websites.
The Hermetica Digital certificate was issued in April 2021, but the time stamp on the malicious code itself was Dec. 28, 2021.
ESET researchers said in a blog post that those dates suggested that “the attack may have been in the works for some time.”
If, as is widely assumed by cybersecurity experts and U.S. defence officials, the attacks were carried out by Russians, then the time stamps are potentially significant data points for observers hoping to understand when the plan for the invasion of Ukraine came together.
ESET’s head of threat research, Jean-Ian Boutin, told Reuters there were various ways in which a malicious actor could fraudulently obtain a code signing certificate.
“They can obviously obtain it themselves, but they can also buy it in the black market,” Boutin said.
“As such, it is possible that the operation dates back further than we previously knew, but it is also possible that the threat actor acquired this code signing certificate recently, just for this campaign.”
Ben Read, director of cyber espionage analysis at Mandiant, said it was possible that a group could “impersonate a company in communications with a digital cert providing company and get a legitimate cert fraudulently issued to them.”
Cybersecurity firm Symantec said organisations in the financial, defence, aviation and IT services sectors had been targeted in Wednesday’s attack. DigiCert, the company that issued the digital certificate, did not immediately respond to a request for comment.
Juan-Andres Guerrero-Saade, a cybersecurity researcher at digital security firm SentinelOne, said the purpose of the attack was clear: “This was meant to damage, disable, signal and cause havoc.”
(Reporting by Michele Kambas in Nicosia, and James Pearson and Raphael Satter in London; Additional reporting by Christopher Bing in Washington; Editing by Matthew Lewis)